3 min read
Vendor Management Tips for 2022
The foundation to a productive business is a complex one. You need several skills working in tandem to execute several tasks on a regular basis.
Read More
3 min read
The foundation to a productive business is a complex one. You need several skills working in tandem to execute several tasks on a regular basis.
Read More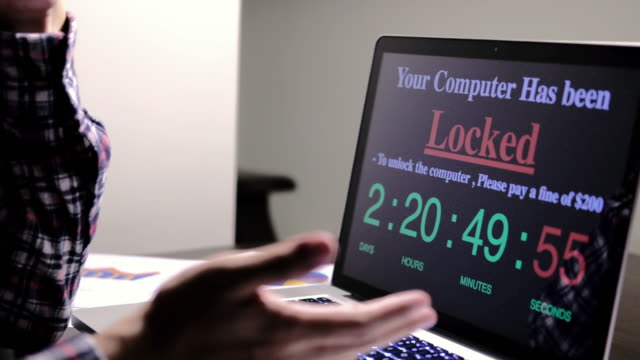
6 min read
In 2020, there were approximately 304 million ransomware attacks worldwide. These types of attacks are an ongoing growing threat for business owners. All it takes is a single...

6 min read
Approximately 74% of organizations in the United States experienced a successful phishing attack last year. Cybercrime has cost individuals and U.S. businesses about $4.2...

5 min read
What is Cybersecurity Risk Management? Cybersecurity risk management is a specialized practice that prioritizes defensive measures for cybersecurity designed to address...

6 min read
If you’ve been researching how to meet certain compliance standards, you may have come across the acronym “POA&M” a few times by now. Or, this may be your first time seeing...

7 min read
Every business today relies on technology and information for every business process. Regardless of industry, tech drives business results. However, this reliance on...

6 min read
Technology is a cornerstone of modern business. IT systems play a key role in most business processes these days. To keep up with new technological developments and stay...

4 min read
IT plays a critical role in modern businesses. Technology solutions empower almost every business process in some way—whether directly or indirectly. However, in many...
4 min read
Many businesses have to work hard to meet different security compliance standards. From DoD contractors who have to meet NIST 800-171 and the Cybersecurity Maturity Model...

5 min read
In November of 2020, the U.S. Department of Defense (DoD) rolled out the interim rule for the cybersecurity maturity model certification (CMMC). This is a major rule change...