Network Firewall Security: How You Can Make Full Use Of It
Cybercrime is having a truly major impact on the global economy, a new report has claimed. According to McAfee, in 2018, cybercrime cost the global...
In 2020, there were approximately 304 million ransomware attacks worldwide. These types of attacks are an ongoing growing threat for business owners. All it takes is a single successful attack to put a business out for days, weeks, or even months.
As attacks can be relentless and devastating, it's essential to know what steps you can take to protect your business before falling victim to them. This article will explain what you can do to protect your business from falling prey to these types of cyberattacks.
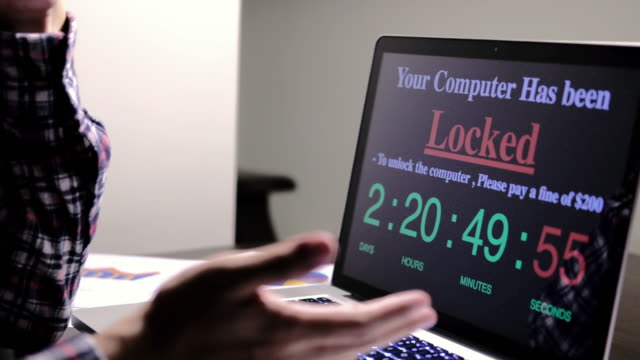
Ransomware is a type of software created by hackers to steal and encrypt essential data from users. As the name suggests, attackers demand a ransom in money in exchange for a "unique key" to unlock the encrypted files.
A ransomware attack can start when the user downloads a corrupted file that spreads through all the OS.
To infect files, hackers use methods like:
Once the malicious software is in the system, it will begin scanning through all the information it deems valuable. After it finds something, it will lock the file and create a unique key. If the user clicks on the file, a pop-up will generate, saying they need to pay to recover it.
In 2019, ransomware from phishing emails increased by 109%. Hackers' most preferred methods to trick users into downloading ransomware are sending files containing PDFs, ZIPs, Word Documents, and Excel spreadsheets.
Once the victims download the attachment, the ransomware can start working immediately. Depending on the malware's configuration, it may take days, weeks, or even months before the malware shows itself.
Microsoft created RDP as a means to help users troubleshoot their computers remotely. However, cybercriminals have taken advantage of this feature and used it to their advantage.
Hackers exploit this software by using brute-force attacks or pretending to be employees for Microsoft and then ask people for personal information. Once they have the data, they can disable the firewall and antivirus to implant files maliciously.
If you are a business owner, you need to watch for new software patches the day they come out; don't wait months years. If you don't, hackers will exploit the lack of security.
Related: 5 Common Cyber Threats To Watch Out For
The beauty of immutable backups is that they cannot be altered or changed. This type of backup is ideally essential for malware and ransomware attacks or unforeseen events.
In case you fall victim to a ransomware attack, an immutable backup can save you from:
It's good practice to back up your data multiple times a day to safeguard your data optimally. Keep at least one backup file offline to ensure hackers didn't infect it. And if the attacker was successful in infecting your devices with ransomware, you need to reset your OS and restore it with the last clean backup you have saved.
If you are not sure how to optimize your security, it's best to hire a specialized security team that guides you to protect your network's endpoints, including:
Ask them about the best practices in today's market to protect your data from cyber theft. They can help you determine which devices you use are a potential entry point for ransomware. They will protect these devices from hackers by:
Hire a professional team like Systems X to get an IT advisory so you can rest assured all your valuable information is being protected.
Related: The Top 5 Benefits of Investing In IT Management Services
Setting automatic updates can save you a lot of manual work and time. Also, keeping software up to date with the latest updates and patches can ensure optimal protection of:
Don't forget that hackers are constantly implementing new methods to steal your information. Waiting too long before you update your system can put your business at serious risk of being exploited.
When it comes to protecting your information, a firewall is an excellent tool for deflecting ransomware attacks. They scan and help the security team monitor any signs of malicious payloads. Firewalls can also allow the security team to watch what comes in and out of your computer.
To best support your firewall defenses, consider setting up:
Your firewall should be able to run a deep (automatic) packet inspection (DPI) scan to examine all the data stored in your computer. This capability can potentially identify infected files.
RELATED: NETWORK FIREWALL SECURITY: HOW YOU CAN MAKE FULL USE OF IT
When employees use their devices without regulations during the office, this can pose unnecessary risks to your network. You can write a new policy that outlines how and when employees can use a device if they need to. Also, make sure that work devices and personal devices don't share the same Wi-Fi network to avoid risks.
Set a meeting with your team and review the importance of having a solid password. The average user uses passwords that are easy to guess. Passwords like abc123 or 123456 are pretty standard.
Remember, all it takes is a single employee who doesn't follow guidelines to put the company at risk. Hackers know this, and they often start exploiting these weaknesses because employees are not taking security seriously enough.
Ensuring that all employees have strong passwords that they update regularly is one of the best security practices. If they don't, cybercriminals can breach your system with a simple brute-force attack.
Another great practice is to use a second-step authentication service. This way, you are ensuring that the right person is accessing the correct information.
Once ransomware enters your system, the malware moves from device to device in your network until it finds the targeted data. Sectioning off the office can prevent infiltrators from freely moving through operating systems.
Make sure each subsystem connected to the network is:
If an intruder gains access to a part of your network, sectioning off prevents them from succeeding in the attack. Since the attackers need time to break into each segment, sectioning off will give the security team time to identify and isolate the threat.
Running regular security checks can help in determining the degree of vulnerability the system has. These assessments enable you to inspect the IT environments for system exploits, such as:
Consider organizing a penetration test if you want to know how well prepared your team is against a ransomware attack. These types of tests can help you see how well your system and staff react to imminent threats.
A reputable ad blocker will help protect you and your loved one's privacy on the internet. They prevent sites from collecting your data and selling it to others. If you constantly surf the web, installing an adblocker is a great way to keep your and your loved ones' information safe online.
They also ensure all employee devices and browsers have plug-ins and extensions that automatically block pop-up ads. Much of the malicious software installed is when users click on an ad redirecting them to an unsecured site. Malicious marketing is a common ransomware source. Getting a paid ad blocker is a simple way to limit the number of attacks your company will deal with.
The management team is the one who organizes your business's protection against unwanted cybercriminals. If it's related to cyber threats, intrusions, malware, and other types of data breaches, a cybersecurity risk management team is the one who can determine what step to take next.
There are many responsibilities that a cyber security manager needs to handle while on the job. Here is a list of the most common tasks a cyber security manager does:

Isolate the infected system to prevent the attacker from controlling the compromised device any further. Turn off the device and the Wi-Fi to cut off the data exfiltration and lateral movement until the problem is solved.
Open your download folder and uninstall any program that you do not recognize. Remove everything on the infected device and try reinstalling the OS.
Once the attack is under control, restore data from the most recent backup available.
Report the security breach to the appropriate department to help the team know what measures to take to mitigate any further cyberattack in the future.
Looking for a professional IT management provider to protect your business's valuable information from hackers? Visit Systems X to learn more about the latest technology trends to protect your data!
The best way to prevent ransomware and keep your business safe is to actively search for new methods in the market to secure your information. The suggestions outlined above can give you a step ahead of hackers to avoid needless monetary losses and reputation damage.

Cybercrime is having a truly major impact on the global economy, a new report has claimed. According to McAfee, in 2018, cybercrime cost the global...

For businesses to function effectively in the current era of massive market competition, it’s essential that they actively utilize the best, most...

Email communication is now what makes the world go ‘round. While the pandemic has exacerbated the need for online communication channels, email has...